Building Network Tools with Scapy
Scapy p.01
Scapy Introduction and Overview
What is Scapy?
No one can introduce Scapy better than the creator of the project himself:
Scapy is a powerful interactive packet manipulation program. It is able to forge or decode packets of a wide number of protocols, send them on the wire, capture them, match requests and replies, and much more. It can easily handle most classical tasks like scanning, tracerouting, probing, unit tests, attacks or network discovery
It also performs very well at a lot of other specific tasks that most other tools can't handle, like sending invalid frames, injecting your own 802.11 frames, combining technics (VLAN hopping+ARP cache poisoning, VOIP decoding on WEP encrypted channel, ...), etc.
- Phil @ secdev.org
Scapy p.02
Installing Python and Scapy
Installing Python
Scapy was originally written for Python 2, but since the 2.4 release (March 2018), you can now use Scapy with Python 3.4+! I will prefer Python 3 in examples but will also include notes about big differences between each python version and Scapy if they exist.
Scapy p.03
Scapy Interactive Mode
Running Scapy
Scapy can be run in two different modes, interactively from a terminal window and programmatically from a Python script. Let's start getting familiar with Scapy using the interactive mode.
Scapy p.04
Looking at Packets
Packets, Layers, and Fields. Oh My!
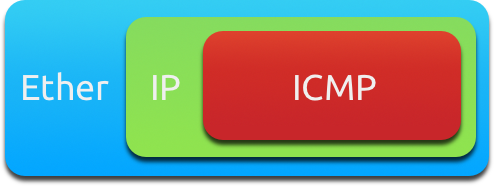
Scapy uses Python dictionaries as the data structure for packets. Each packet is a collection of nested dictionaries with each layer being a child dictionary of the previous layer, built from the lowest layer up. Visualizing the nested packet layers would look something like this:
Scapy p.05
Sending our First Packet; ARP Response
With a good understanding of how to view our packets we can now move onto some packet generation. Let's talk a bit about sniffing first and how existing packets are our best tool for creating new ones.
Scapy p.06
Sending and Receiving with Scapy
We've sniffed some packets, dig down into packet layers and fields, and even sent some packets. Great job! It's time to step up our game with Scapy and start really using some of the power Scapy contains. Please Note: this next example is for education and example only. Please be responsible on your network, especially at work!
Scapy p.07
Monitoring ARP
Using Scapy in a Python Script
So far we've been working with Scapy in interactive mode. It's very powerful but there are times when it would be easier to work with a Python script instead. In order to use Scapy, we have to import the Scapy module like this:
from scapy.all import *
This will import all Scapy functions, but if you know that you will only need a few of the functions, you can import them individually as well like this:
from scapy.all import sr1,IP,ICMP
Scapy p.08
Making a Christmas Tree Packet
We've doing a lot of packet sniffing, analysis, and even some basic packet crafting of our own. With the ICMP packets we created, we only set the destination we wanted to use and let Scapy take care of the rest.
Scapy p.09
Scapy and DNS
We've been able to work with Ethernet, ARP, IP, ICMP, and TCP pretty easily so far thanks to Scapy's built in protocol support. Next on our list of protocols to work with are UDP and DNS.
DNS Request and Response
Using the sr1() function, we can craft a DNS request and capture the returned DNS response.
Scapy p.10
Emulating nmap Functions
We've seen a lot of cool applications for scapy in your network tools, but a good inspiration for new tools is to look at existing tools to figure out how they do their job. We will be emulating some nmap & Angry IP Scanner type features and creating the following tools:
Scapy p.11
Scapy Resources
I hope you had as much fun as I did getting started with Scapy. These are all starter ideas, but we've barely uncovered the tip of the iceberg. I'll continue to write articles about cool Scapy tools I come up with but you should dig into the docs below and see what you find. If you have any questions or comments about this guide, feel free to contact me.